[caption id="attachment_14425" align="aligncenter" width="473"]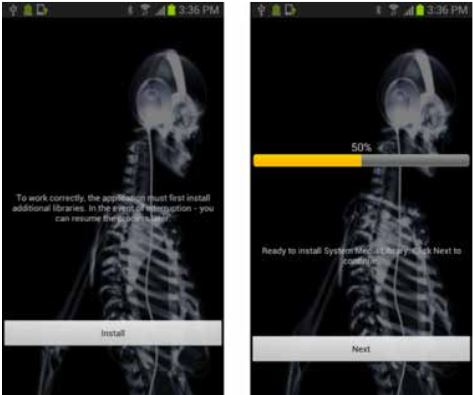 Android/Repane malware downloads malicious payload, not X-ray capabilities.[/caption] Malware and spam are on the rise for both PCs and mobile devices, but it's not the number of malicious apps that are the problem. The real problem, according to McAfee Labs' newest online threat report, is that malware developers have gotten so good at faking digital certifications that it is becoming increasingly perilous to rely on digital signatures to decide whether an application is trustworthy or not. The number of malicious apps carrying digital signatures increased by 50 percent, to more than 1.5 million, during the third quarter of 2013, according to McAfee Labs Threats Report: Third Quarter 2013 (PDF), which was posted Nov. 21. Demand from malware developers for ways to duck verification on mobile devices is so intense, in fact, that a new family of malware that allows other apps to bypass digital-signature validation on Android devices helped boost the volume of Android-based malicious apps by 33 percent, to a total of 680,000 during the third quarter of 2013, according to the report. The total count is higher than any other quarter since McAfee began tracking Android malware during the second quarter of 2011, except for Q4 2012, when the count passed 900,000 for the first and only time so far. Malware aimed at Apple's iOS is becoming more common but is still "insignificant" by comparison with Android, the report added. The newest high-threat family of malicious Android apps – Exploit/MasterKey.A – allows malware installing itself on Android devices to avoid the digital-signature validation process that is a core part of Android security for both documents and apps. A second family of malicious apps – which is also new – installs itself and then downloads a second payload without the user's knowledge. The two represent both an increasingly large economy of specialized malware developers and a specific technique to avoid identification by breaking a single malicious app into separate modules to make the activity of each look less threatening. The Android/Repane family, for example, contains a downloader whose only job is to get itself installed by posing as an app that takes X-rays with a cell-phone camera. When it's launched it actually downloads a second payload, in this case one that collects user information and sends it to the attacker. Among all forms of malware, the number of rootkits doubled during the quarter, 20 million new bits of malware appeared and ransomware such as Cryptolocker – which lock up files or a whole system until the owner pays to have it removed – are also rising rapidly. Among platform-specific threats, the number of malicious apps aimed at mobile devices rose 33 percent during the quarter. Threats from suspicious or malicious web sites increased 14 percent. Browser threats using hidden iframes, malicious embedded Java code or other techniques make up nearly half of all online malicious activity, the McAfee survey found. Though far less of a threat than malware, the volume of spam continues to rise as well, with more than 4 trillion spam messages appearing in September alone – the highest level since 2010. Undermining digital certificates doesn't just open a few doors for a few malicious apps; it attacks one of the few technologies available to verify the contents or validity of a file transported across the Internet, and threatens the ability of Internet users to exchange anything digital with any level of equanimity. "The efforts to bypass code validation on mobile devices, and commandeer it altogether on PCs, both represent attempts to circumvent trust mechanisms upon which our digital ecosystems rely," according to Vincent Weafer, senior vice president of McAfee Labs, as quoted in the McAfee statement announcing the most recent report. Weakened confidence in the contents of files routinely exchanged in the course of consumer e-commerce or B2B collaboration throws a shadow over the financial future of the Web just as demand is ramping up for Bitcoin and other forms of digital money or ways to exchange value. "As these currencies become further integrated into our global financial system, their stability and safety will require both financial monetary controls and oversight," Weafer said. "The industry must work harder to ensure the integrity of these technologies given they are becoming more pervasive in every aspect of our daily lives." Image:McAfee Labs
Android/Repane malware downloads malicious payload, not X-ray capabilities.[/caption] Malware and spam are on the rise for both PCs and mobile devices, but it's not the number of malicious apps that are the problem. The real problem, according to McAfee Labs' newest online threat report, is that malware developers have gotten so good at faking digital certifications that it is becoming increasingly perilous to rely on digital signatures to decide whether an application is trustworthy or not. The number of malicious apps carrying digital signatures increased by 50 percent, to more than 1.5 million, during the third quarter of 2013, according to McAfee Labs Threats Report: Third Quarter 2013 (PDF), which was posted Nov. 21. Demand from malware developers for ways to duck verification on mobile devices is so intense, in fact, that a new family of malware that allows other apps to bypass digital-signature validation on Android devices helped boost the volume of Android-based malicious apps by 33 percent, to a total of 680,000 during the third quarter of 2013, according to the report. The total count is higher than any other quarter since McAfee began tracking Android malware during the second quarter of 2011, except for Q4 2012, when the count passed 900,000 for the first and only time so far. Malware aimed at Apple's iOS is becoming more common but is still "insignificant" by comparison with Android, the report added. The newest high-threat family of malicious Android apps – Exploit/MasterKey.A – allows malware installing itself on Android devices to avoid the digital-signature validation process that is a core part of Android security for both documents and apps. A second family of malicious apps – which is also new – installs itself and then downloads a second payload without the user's knowledge. The two represent both an increasingly large economy of specialized malware developers and a specific technique to avoid identification by breaking a single malicious app into separate modules to make the activity of each look less threatening. The Android/Repane family, for example, contains a downloader whose only job is to get itself installed by posing as an app that takes X-rays with a cell-phone camera. When it's launched it actually downloads a second payload, in this case one that collects user information and sends it to the attacker. Among all forms of malware, the number of rootkits doubled during the quarter, 20 million new bits of malware appeared and ransomware such as Cryptolocker – which lock up files or a whole system until the owner pays to have it removed – are also rising rapidly. Among platform-specific threats, the number of malicious apps aimed at mobile devices rose 33 percent during the quarter. Threats from suspicious or malicious web sites increased 14 percent. Browser threats using hidden iframes, malicious embedded Java code or other techniques make up nearly half of all online malicious activity, the McAfee survey found. Though far less of a threat than malware, the volume of spam continues to rise as well, with more than 4 trillion spam messages appearing in September alone – the highest level since 2010. Undermining digital certificates doesn't just open a few doors for a few malicious apps; it attacks one of the few technologies available to verify the contents or validity of a file transported across the Internet, and threatens the ability of Internet users to exchange anything digital with any level of equanimity. "The efforts to bypass code validation on mobile devices, and commandeer it altogether on PCs, both represent attempts to circumvent trust mechanisms upon which our digital ecosystems rely," according to Vincent Weafer, senior vice president of McAfee Labs, as quoted in the McAfee statement announcing the most recent report. Weakened confidence in the contents of files routinely exchanged in the course of consumer e-commerce or B2B collaboration throws a shadow over the financial future of the Web just as demand is ramping up for Bitcoin and other forms of digital money or ways to exchange value. "As these currencies become further integrated into our global financial system, their stability and safety will require both financial monetary controls and oversight," Weafer said. "The industry must work harder to ensure the integrity of these technologies given they are becoming more pervasive in every aspect of our daily lives." Image:McAfee Labs

