[caption id="attachment_13243" align="aligncenter" width="585"]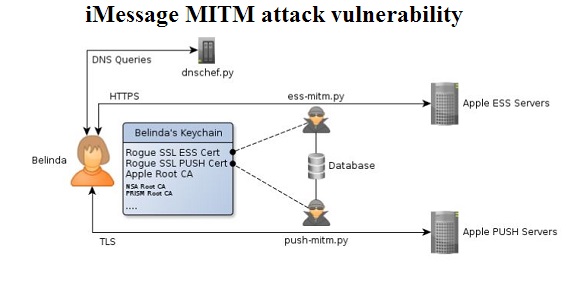 Researchers found vulnerabilities in Apple's iMessage protocol[/caption] Using the iMessage text protocol and application that Apple promised would keep users safe from the NSA turns out not to be so safe – against the NSA or against Apple itself, according to one iOS jailbreaker and security researcher. Apple's claim that both iMessage and FaceTime are protected by end-to-end encryption controlled by the end user and unbreakable even by Apple are "just basically lies," according to Cyril Cattiaux, who presented his findings at Hack in the Box, a security conference in Kuala Lumpur and was quoted Oct. 17 by the IDG News Service. Cattiaux, who has written iOS jailbreak applications and who works for French penetration-testing company Quarkslab, dissected the iMessage protocol and authentication to conclude that Apple itself can break iMessage encryption at any time... and the NSA probably can as well. Cattiaux' presentation is posted here. That directly contradicts Apple's own statement on its encryption: "Apple has always placed a priority on protecting our customers’ personal data, and we don’t collect or maintain a mountain of personal details about our customers in the first place," Apple promised in a statement posted June 16 that restated its opposition to NSA snooping and its confidence in its own security. "For example, conversations which take place over iMessage and FaceTime are protected by end-to-end encryption so no one but the sender and receiver can see or read them. Apple cannot decrypt that data." There is encryption from one end to the other of the iMessage process, but the way Apple built the key infrastructure makes iMessages vulnerable in many ways, Cattiaux wrote in a blog posted Oct. 17. The encryption between iMessage clients and Apple servers during the encryption process is very strong– "preventing the development of 3rd party iMessage clients" – Cattiaux wrote. The rest of the process has a few weaknesses. First, all the traffic goes through Apple's servers, which supply the encryption keys. By saving the keys and sending fake authentications to the clients involved, Apple can read an iMessage stream or even intercept, modify and re-send it without any indication security had been violated, Cattiaux wrote. Apple's mobile-device management also gives an iPhone user's employer surprisingly insecure access. Devices connected to the iPhone Configuration Utility – Apple's enterprise iPhone management application – get a second security certificate controlled by the company that is trusted in all encrypted SSL connections the device makes afterward. With the certificate and a proxy that re-routes SSL connections through a proxy server, employers can see all the unencrypted text traveling between the Apple device and Apple's servers. User passwords travel through SSL connections to iMessage servers, but they travel in clear text, so employers could easily collect the AppleIDs and passwords of all their iMessage-using employees. "Apple's claim that they cant read end-to-end encrypted iMessage is definitely not true. As everyone suspected: yes they can!," Cattiaux wrote. "It seems that [Apple has] pretty much unfettered ability — technologically — to eavesdrop if they wanted to," according to cryptography researcher and Johns Hopkins University Information Security Institute Professor Matthew Green, one of two researchers Mashable asked to examine and confirm Cattiaux' findings for an Oct. 17 article. Apple declined the IDG News Service request for a comment or clarification. Cattiaux called for Apple to make its public-key-infrastructure and authentication process more transparent. He also said the weaknesses weren't as bad as those in many mobile apps, and that iMessage was a decent option for anyone not sending information they genuinely expected to remain top secret: "MITM attacks on iMessage are unpractical to the average hacker, and the privacy of iMessage is good enough for the average user." Image:/ Cyril Cattiaux/QuarksLab
Researchers found vulnerabilities in Apple's iMessage protocol[/caption] Using the iMessage text protocol and application that Apple promised would keep users safe from the NSA turns out not to be so safe – against the NSA or against Apple itself, according to one iOS jailbreaker and security researcher. Apple's claim that both iMessage and FaceTime are protected by end-to-end encryption controlled by the end user and unbreakable even by Apple are "just basically lies," according to Cyril Cattiaux, who presented his findings at Hack in the Box, a security conference in Kuala Lumpur and was quoted Oct. 17 by the IDG News Service. Cattiaux, who has written iOS jailbreak applications and who works for French penetration-testing company Quarkslab, dissected the iMessage protocol and authentication to conclude that Apple itself can break iMessage encryption at any time... and the NSA probably can as well. Cattiaux' presentation is posted here. That directly contradicts Apple's own statement on its encryption: "Apple has always placed a priority on protecting our customers’ personal data, and we don’t collect or maintain a mountain of personal details about our customers in the first place," Apple promised in a statement posted June 16 that restated its opposition to NSA snooping and its confidence in its own security. "For example, conversations which take place over iMessage and FaceTime are protected by end-to-end encryption so no one but the sender and receiver can see or read them. Apple cannot decrypt that data." There is encryption from one end to the other of the iMessage process, but the way Apple built the key infrastructure makes iMessages vulnerable in many ways, Cattiaux wrote in a blog posted Oct. 17. The encryption between iMessage clients and Apple servers during the encryption process is very strong– "preventing the development of 3rd party iMessage clients" – Cattiaux wrote. The rest of the process has a few weaknesses. First, all the traffic goes through Apple's servers, which supply the encryption keys. By saving the keys and sending fake authentications to the clients involved, Apple can read an iMessage stream or even intercept, modify and re-send it without any indication security had been violated, Cattiaux wrote. Apple's mobile-device management also gives an iPhone user's employer surprisingly insecure access. Devices connected to the iPhone Configuration Utility – Apple's enterprise iPhone management application – get a second security certificate controlled by the company that is trusted in all encrypted SSL connections the device makes afterward. With the certificate and a proxy that re-routes SSL connections through a proxy server, employers can see all the unencrypted text traveling between the Apple device and Apple's servers. User passwords travel through SSL connections to iMessage servers, but they travel in clear text, so employers could easily collect the AppleIDs and passwords of all their iMessage-using employees. "Apple's claim that they cant read end-to-end encrypted iMessage is definitely not true. As everyone suspected: yes they can!," Cattiaux wrote. "It seems that [Apple has] pretty much unfettered ability — technologically — to eavesdrop if they wanted to," according to cryptography researcher and Johns Hopkins University Information Security Institute Professor Matthew Green, one of two researchers Mashable asked to examine and confirm Cattiaux' findings for an Oct. 17 article. Apple declined the IDG News Service request for a comment or clarification. Cattiaux called for Apple to make its public-key-infrastructure and authentication process more transparent. He also said the weaknesses weren't as bad as those in many mobile apps, and that iMessage was a decent option for anyone not sending information they genuinely expected to remain top secret: "MITM attacks on iMessage are unpractical to the average hacker, and the privacy of iMessage is good enough for the average user." Image:/ Cyril Cattiaux/QuarksLab