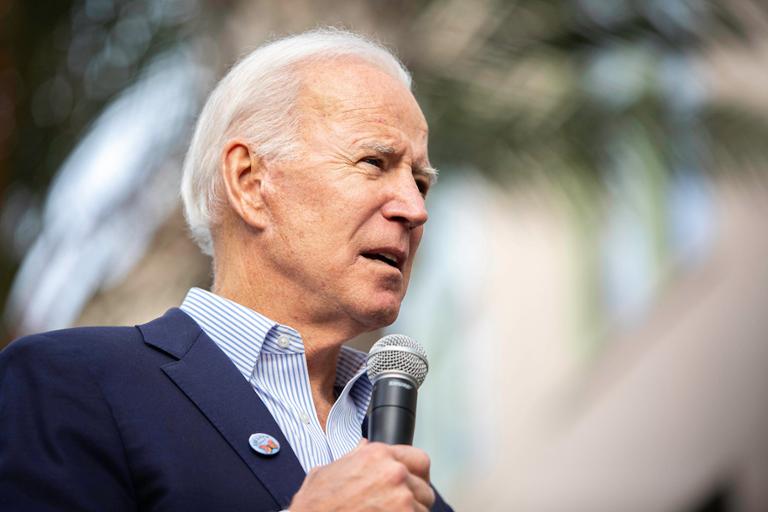
President Joe Biden signed a $1 trillion bipartisan infrastructure spending bill into law on Nov. 15. The White House wants to use the legislation to invest vast amounts of money to build and repair roads, bridges and other parts of the nation’s physical infrastructure. Cybersecurity could also benefit.
Speaking at the White House Monday, Biden noted that the bill is one way to keep up with the technological innovations of other countries, including China, that have also invested billions in these types of projects.
“For most of the 20th century, we led the world by a significant margin because we invested in ourselves. But somewhere along the way, we stopped investing in ourselves. We’ve risked losing our edge as a nation, and China and the rest of the world are catching up,” Biden said.
Tucked inside the massive spending bill (officially called the Infrastructure Investment and Jobs Act) are billions of dollars earmarked to address another growing concern: cybersecurity. Once enacted, experts say that the infrastructure legislation will likely pave the way for private businesses and government agencies, especially those at the state and local level, to invest in both the hiring of more security talent as well as giving these organizations the ability to purchase newer technologies designed to address modern threats.
Among the various provisions in the infrastructure bill, there’s money set aside for specific cybersecurity spending, including:
- $1 billion for state, local, tribal and territorial governments to modernize their IT networks and infrastructure to better respond to modern threats such as ransomware attacks. The money from this portion of the bill will be spread out across the next four years.
- $100 million in spending over five years to help create a cyber response and recovery fund that the private-sector owners and operators of U.S. critical infrastructure can tap into following a cyber incident.
- $21 million for staffing for the Office of the National Cyber Director.
While most of the money available to state and local government agencies comes in the form of grants, the way the bill is written means that these entities can use the dollars in more creative ways, including investing in managed security services—an acknowledgment of how difficult it is to fully staff cybersecurity response teams and operations centers, said Mike Hamilton, the former vice chair for the U.S. Department of Homeland Security's State, Local, Tribal, and Territorial Government Coordinating Council, who also served as the CISO of Seattle.
“This is likely an acknowledgment of the difficulty in staffing security—especially for 24/7/365 monitoring, which has become a key requirement that insurance companies want to see in place,” Hamilton, who is now the CISO of security firm Critical Insight, told Dice. “Grant-funded managed detection and response and managed extended detection and response can be a game-changer for local governments.”
Federal Dollars; Local Development
The spending on cyber is also not done. The other major piece of Biden legislation still under debate in Congress, the Build Back Better bill, contains $500 million for additional cybersecurity funding for the U.S. Cybersecurity and Infrastructure Security Agency, as well as money to improve cloud and industrial control system security.
As they develop their grant proposals over the coming months and years, state and local government agencies will shape how the specific cybersecurity portions of the bill will be spent. Still, the attention that the infrastructure bill and other legislation is focusing on cyber is likely to encourage more spending on developing staff with specialized skills, said Bill O’Neill, vice president of public sector at security firm ThycoticCentrify.
“What particularly stands out to me is just how big of focus cybersecurity is within the bill—especially as it pertains to critical infrastructure. Also, the added funding it’ll afford to U.S. Cyber Command and CISA is a massive win for the country’s cyber defense strategy,” O’Neill told Dice.
“It will allow these organizations to create broader, more robust policies, as well as extend their planning and tactical projections much further in advance to implement better cybersecurity measures from the highest levels of government, down to state and local municipalities,” O’Neill added. “This bill will help ensure that those plans are designed for long-term goals and are sufficiently funded to reach them.”
Getting the Cybersecurity Resources
While some studies have shown an increase in cybersecurity hiring over the last two years, there are still tens of thousands of open positions and skilled workers needed for an increasingly critical industry. Cyber Seek, a job-tracking database developed by the Department of Commerce and CompTIA, estimates there are 465,000 open cyber positions across the U.S., with about 36,000 of these positions open across federal, state and local government agencies.
(On the same day Biden signed the infrastructure bill, the Department of Homeland Security announced a new hiring portal to help bring more cyber talent into the federal government.)
And while the infrastructure bill does not specifically address issues of staffing and hiring, several experts see the legislation as opening doors to more training programs and other projects that can bring talent into the cybersecurity sector—or re-skill those who want to expand a career, especially at the local level.
“Tying new cyber-related programs to the infrastructure bill will lead to a marked increase in cyber-hiring in the infrastructure industry, notably at Transportation Security Administration and state-level transportation departments,” Victoria Mosby, a federal sales engineer at security firm Lookout, told Dice. “This trickle-down effect could lead to the promotion of increased state-level cyber education programs, job fairs and signing incentives to attract cyber talent away from the federal government and private sector.”
Mosby also sees grant money flowing to community colleagues and state-run universities to help develop either new curriculum related to cybersecurity or certifications programs to open doors to potential recruits.
O’Neill noted that the influx of federal money to state, local and tribal agencies is also likely to ensure that security professionals are up-to-date on the latest concepts such as zero trust.
“A critical advanced-level cybersecurity training program will be funded through this bill. This includes federal agencies and critical infrastructure focus. We are seeing specialized degrees for cybersecurity, which include focused areas in zero trust security best practices,” O’Neill said.
Not everyone is convinced, however. John Bambenek, a principal threat hunter at Netenrich, noted that, without more specifics, the money might go to consultants who are advising city and state agencies, but not toward hiring those professionals who can solve day-to-day problems.
“One-time funds typically don’t result in a large influx of professionals being hired. Perhaps consultants, who are used to temporary engagements, will see this money but overall, this bill doesn’t address the core problem of lowering the bar of entry for new professionals or increasing training opportunities for existing ones,” Bambenek told Dice. “There was a large one-time expenditure for election cybersecurity, but outside specific places, there didn’t seem to be a large influx of new permanent employees into government as a result.”
Hamilton, who has experience working with local agencies on grant proposals, noted that if hiring more staff isn’t in the cards, organizations can upgrade their existing technologies, such as Microsoft Defender, by upgrading licenses that allow for more protection in cloud environments.
“I would also request improvements in upgrading deprecated operating systems and applications and improvements to end-point agents—if needed—to gain user behavior baselining and rapid remote quarantine capabilities,” Hamilton said. “If I was a government organization that uses Microsoft Defender as an endpoint, I’d spend the money on upgrading to E5 licenses to gain the cloud AI, [Microsoft Cloud App Security] logging, etc., which turns Defender into more of a Crowdstrike without having to replace agents on everything.”


