 Google will offer additional rewards for functional exploits, including any that lead to “kernel compromise from an installed app or with physical access to the device” (payouts could total an additional $10,000). Discovery of a “remote or proximal attack vector” can earn the researcher up to $20,000. Google is also interested in exploits or chains of exploits leading to TEE (TrustZone) or Verified Boot compromise from an installed app or physical access to a device. “All bugs should be reported to AOSP's public bug tracker using the Security Bug Report template,” Google wrote in the program announcement. “If you are submitting a patch or CTS test, please attach the patches to the bug report instead of uploading them directly to AOSP.” The company warned developers and researchers to only attempt a vulnerability investigation on a device they actually own, which is great advice—nobody likes it when you crack their phone without permission.
Google will offer additional rewards for functional exploits, including any that lead to “kernel compromise from an installed app or with physical access to the device” (payouts could total an additional $10,000). Discovery of a “remote or proximal attack vector” can earn the researcher up to $20,000. Google is also interested in exploits or chains of exploits leading to TEE (TrustZone) or Verified Boot compromise from an installed app or physical access to a device. “All bugs should be reported to AOSP's public bug tracker using the Security Bug Report template,” Google wrote in the program announcement. “If you are submitting a patch or CTS test, please attach the patches to the bug report instead of uploading them directly to AOSP.” The company warned developers and researchers to only attempt a vulnerability investigation on a device they actually own, which is great advice—nobody likes it when you crack their phone without permission. Google Will Pay You to Hunt Android Bugs
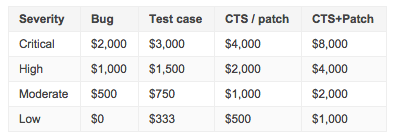
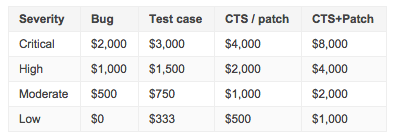
Android developers and software researchers, Google wants to pay you to hunt some bugs. Earlier this year, Google announced that it would pay out up-front rewards to researchers to hunt bugs throughout some of its various Web services and apps. Now it’s preparing to shell out cash to those researchers who disclose vulnerabilities to the Android Security Team. The program will cover the latest available Android versions for Nexus phones and tablets currently for sale in Google’s online storefront (i.e., the Nexus 6 and Nexus 9). Payouts are based on the severity of the bugs; a "critical" one could net anywhere from $2,000 to $8,000, depending on whether the researcher submits a patch or CTS test along with the bug report. Bugs rated “high severity” can earn a researcher up to $4,000 (with patch and CTS test), while "moderate" bugs are good for $2,000. A "low-severity" bug is worth up to $1,000. 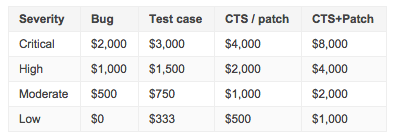 Google will offer additional rewards for functional exploits, including any that lead to “kernel compromise from an installed app or with physical access to the device” (payouts could total an additional $10,000). Discovery of a “remote or proximal attack vector” can earn the researcher up to $20,000. Google is also interested in exploits or chains of exploits leading to TEE (TrustZone) or Verified Boot compromise from an installed app or physical access to a device. “All bugs should be reported to AOSP's public bug tracker using the Security Bug Report template,” Google wrote in the program announcement. “If you are submitting a patch or CTS test, please attach the patches to the bug report instead of uploading them directly to AOSP.” The company warned developers and researchers to only attempt a vulnerability investigation on a device they actually own, which is great advice—nobody likes it when you crack their phone without permission.
Google will offer additional rewards for functional exploits, including any that lead to “kernel compromise from an installed app or with physical access to the device” (payouts could total an additional $10,000). Discovery of a “remote or proximal attack vector” can earn the researcher up to $20,000. Google is also interested in exploits or chains of exploits leading to TEE (TrustZone) or Verified Boot compromise from an installed app or physical access to a device. “All bugs should be reported to AOSP's public bug tracker using the Security Bug Report template,” Google wrote in the program announcement. “If you are submitting a patch or CTS test, please attach the patches to the bug report instead of uploading them directly to AOSP.” The company warned developers and researchers to only attempt a vulnerability investigation on a device they actually own, which is great advice—nobody likes it when you crack their phone without permission.
 Google will offer additional rewards for functional exploits, including any that lead to “kernel compromise from an installed app or with physical access to the device” (payouts could total an additional $10,000). Discovery of a “remote or proximal attack vector” can earn the researcher up to $20,000. Google is also interested in exploits or chains of exploits leading to TEE (TrustZone) or Verified Boot compromise from an installed app or physical access to a device. “All bugs should be reported to AOSP's public bug tracker using the Security Bug Report template,” Google wrote in the program announcement. “If you are submitting a patch or CTS test, please attach the patches to the bug report instead of uploading them directly to AOSP.” The company warned developers and researchers to only attempt a vulnerability investigation on a device they actually own, which is great advice—nobody likes it when you crack their phone without permission.
Google will offer additional rewards for functional exploits, including any that lead to “kernel compromise from an installed app or with physical access to the device” (payouts could total an additional $10,000). Discovery of a “remote or proximal attack vector” can earn the researcher up to $20,000. Google is also interested in exploits or chains of exploits leading to TEE (TrustZone) or Verified Boot compromise from an installed app or physical access to a device. “All bugs should be reported to AOSP's public bug tracker using the Security Bug Report template,” Google wrote in the program announcement. “If you are submitting a patch or CTS test, please attach the patches to the bug report instead of uploading them directly to AOSP.” The company warned developers and researchers to only attempt a vulnerability investigation on a device they actually own, which is great advice—nobody likes it when you crack their phone without permission.