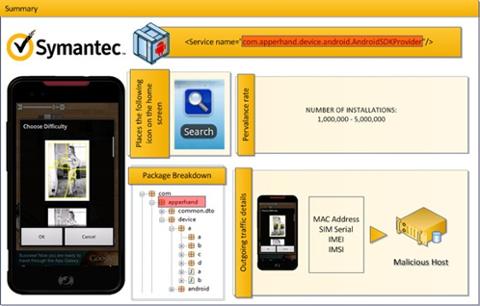
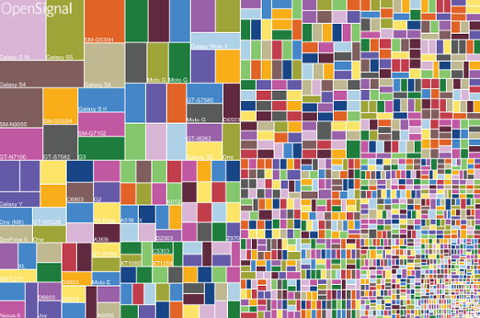
 A vulnerability in Google Android’s security model could give attackers access to hundreds of millions of devices manufactured over the past four years, according to security firm Bluebox Security. Once installed on a device, this Trojan application could access the user’s applications and data—everything from email and documents to account and service passwords. Want to turn on the camera, send emails, or place an unauthorized call to Timbuktu? This vulnerability can supposedly make that happen. “This vulnerability, around at least since the release of Android 1.6 (codename: ‘Donut’), could affect any Android phone released in the last 4 years—or nearly 900 million devices,” Jeff Forristal, CTO of Bluebox, wrote in a corporate blog posting, “and depending on the type of application, a hacker can exploit the vulnerability for anything from data theft to creation of a mobile botnet.” Increasing the risk, he added, are the number of applications—many of them developed by Android device manufacturers, or third parties such as Cisco that work in cooperation with those manufacturers—that have special elevated privileges within the Android ecosystem, “specifically System UID access.” In theory, an attacker could use a Trojan app to hack into multiple devices and bind them together in a zombie “botnet,” similar to what happens on a depressingly regular basis with PCs. The vulnerability, Forristal explained, “involves discrepancies in how Android applications are cryptographically verified & installed, allowing for APK code modification without breaking the cryptographic signature.” In other words, the attacker can alter an application’s code without alerting Android to the change. Forristal plans on sharing more details about the vulnerability during his Black Hat USA 2013 talk. In the interim, he advises Android device owners to be “extra cautious in identifying the publisher of the app they want to download.” Businesses should also caution any and all Android-using employees to update their respective devices. But ultimately it’ll be up to the device manufacturers to ensure that the appropriate firmware updates are released to close the loophole. Bluebox registered the vulnerability with Google in February 2013, as Android security bug 8219321. Image: Google
A vulnerability in Google Android’s security model could give attackers access to hundreds of millions of devices manufactured over the past four years, according to security firm Bluebox Security. Once installed on a device, this Trojan application could access the user’s applications and data—everything from email and documents to account and service passwords. Want to turn on the camera, send emails, or place an unauthorized call to Timbuktu? This vulnerability can supposedly make that happen. “This vulnerability, around at least since the release of Android 1.6 (codename: ‘Donut’), could affect any Android phone released in the last 4 years—or nearly 900 million devices,” Jeff Forristal, CTO of Bluebox, wrote in a corporate blog posting, “and depending on the type of application, a hacker can exploit the vulnerability for anything from data theft to creation of a mobile botnet.” Increasing the risk, he added, are the number of applications—many of them developed by Android device manufacturers, or third parties such as Cisco that work in cooperation with those manufacturers—that have special elevated privileges within the Android ecosystem, “specifically System UID access.” In theory, an attacker could use a Trojan app to hack into multiple devices and bind them together in a zombie “botnet,” similar to what happens on a depressingly regular basis with PCs. The vulnerability, Forristal explained, “involves discrepancies in how Android applications are cryptographically verified & installed, allowing for APK code modification without breaking the cryptographic signature.” In other words, the attacker can alter an application’s code without alerting Android to the change. Forristal plans on sharing more details about the vulnerability during his Black Hat USA 2013 talk. In the interim, he advises Android device owners to be “extra cautious in identifying the publisher of the app they want to download.” Businesses should also caution any and all Android-using employees to update their respective devices. But ultimately it’ll be up to the device manufacturers to ensure that the appropriate firmware updates are released to close the loophole. Bluebox registered the vulnerability with Google in February 2013, as Android security bug 8219321. Image: Google Android Vulnerability Could Affect 900 Million Devices
 A vulnerability in Google Android’s security model could give attackers access to hundreds of millions of devices manufactured over the past four years, according to security firm Bluebox Security. Once installed on a device, this Trojan application could access the user’s applications and data—everything from email and documents to account and service passwords. Want to turn on the camera, send emails, or place an unauthorized call to Timbuktu? This vulnerability can supposedly make that happen. “This vulnerability, around at least since the release of Android 1.6 (codename: ‘Donut’), could affect any Android phone released in the last 4 years—or nearly 900 million devices,” Jeff Forristal, CTO of Bluebox, wrote in a corporate blog posting, “and depending on the type of application, a hacker can exploit the vulnerability for anything from data theft to creation of a mobile botnet.” Increasing the risk, he added, are the number of applications—many of them developed by Android device manufacturers, or third parties such as Cisco that work in cooperation with those manufacturers—that have special elevated privileges within the Android ecosystem, “specifically System UID access.” In theory, an attacker could use a Trojan app to hack into multiple devices and bind them together in a zombie “botnet,” similar to what happens on a depressingly regular basis with PCs. The vulnerability, Forristal explained, “involves discrepancies in how Android applications are cryptographically verified & installed, allowing for APK code modification without breaking the cryptographic signature.” In other words, the attacker can alter an application’s code without alerting Android to the change. Forristal plans on sharing more details about the vulnerability during his Black Hat USA 2013 talk. In the interim, he advises Android device owners to be “extra cautious in identifying the publisher of the app they want to download.” Businesses should also caution any and all Android-using employees to update their respective devices. But ultimately it’ll be up to the device manufacturers to ensure that the appropriate firmware updates are released to close the loophole. Bluebox registered the vulnerability with Google in February 2013, as Android security bug 8219321. Image: Google
A vulnerability in Google Android’s security model could give attackers access to hundreds of millions of devices manufactured over the past four years, according to security firm Bluebox Security. Once installed on a device, this Trojan application could access the user’s applications and data—everything from email and documents to account and service passwords. Want to turn on the camera, send emails, or place an unauthorized call to Timbuktu? This vulnerability can supposedly make that happen. “This vulnerability, around at least since the release of Android 1.6 (codename: ‘Donut’), could affect any Android phone released in the last 4 years—or nearly 900 million devices,” Jeff Forristal, CTO of Bluebox, wrote in a corporate blog posting, “and depending on the type of application, a hacker can exploit the vulnerability for anything from data theft to creation of a mobile botnet.” Increasing the risk, he added, are the number of applications—many of them developed by Android device manufacturers, or third parties such as Cisco that work in cooperation with those manufacturers—that have special elevated privileges within the Android ecosystem, “specifically System UID access.” In theory, an attacker could use a Trojan app to hack into multiple devices and bind them together in a zombie “botnet,” similar to what happens on a depressingly regular basis with PCs. The vulnerability, Forristal explained, “involves discrepancies in how Android applications are cryptographically verified & installed, allowing for APK code modification without breaking the cryptographic signature.” In other words, the attacker can alter an application’s code without alerting Android to the change. Forristal plans on sharing more details about the vulnerability during his Black Hat USA 2013 talk. In the interim, he advises Android device owners to be “extra cautious in identifying the publisher of the app they want to download.” Businesses should also caution any and all Android-using employees to update their respective devices. But ultimately it’ll be up to the device manufacturers to ensure that the appropriate firmware updates are released to close the loophole. Bluebox registered the vulnerability with Google in February 2013, as Android security bug 8219321. Image: Google