The world of cybersecurity changed for good on Dec. 13, 2020.
On that day, incident response firm FireEye Mandiant released the first of several security research reports detailing how a nation-state threat group initially targeted IT software firm SolarWinds as part of a sophisticated supply chain attack. The goal, the analysis noted, was to compromise the company’s infrastructure and create a Trojanized software update for the company’s Orion network monitoring product. This malicious update contained a backdoor, dubbed Sunburst.
Initially, about 18,000 Orion customers downloaded the software update, which installed the Sunburst code within their networks. From there, the group behind the attack deployed other malware variants and eventually focused their main efforts on about 100 prominent private firms as well as nine U.S. government agencies, including the Departments of Homeland Security, State, Energy, Commerce and Justice. Investigators later suspected that the attack was likely a cyberespionage campaign designed to steal emails and other sensitive communication data.
The attack itself appears to have started sometime in early 2020 (although the planning and initial execution might have begun in 2019) and might have continued if FireEye hadn’t discovered it was also a victim and then alerted federal authorities before making the public announcement.
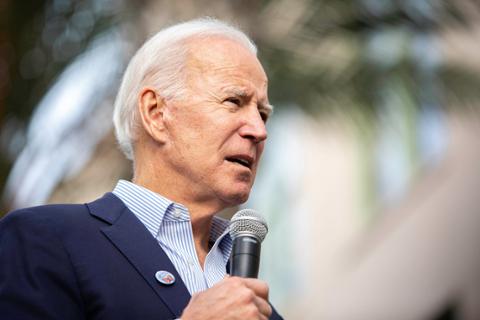
The incident rocketed cybersecurity up the list of priorities for the incoming Biden administration. Later in the year, the White House would publish an executive order outlining dozens of new measures that federal departments would need to adapt to improve their security posture, including how these agencies buy and evaluate third-party software.
The Biden administration also placed blame for the attack on the Russian government, specifically a threat group working within that country’s Foreign Intelligence Service, or SVR, and named by various security researchers as APT29, Cozy Bear and Nobelium. As part of the attribution, the U.S. Treasury Departmentannounced sanctions against several Russia-based individuals and organizations in April.
While some aspects of the SolarWinds attacks are known, many questions are still left unanswered, as multiple investigations continue a year later. The big lesson: even with the added emphasis, supply chains remain vulnerable to attacks, and more needs to be done to shore up cybersecurity.
“One year after the SolarWinds attack, the cyber threat from our foreign adversaries is still as present as ever,” Austin Berglas, who formerly worked as an assistant special agent in charge of cyber investigations at the FBI's New York office, told Dice. “If the reported attribution is correct, the SolarWinds attack not only demonstrated that global infrastructure is still incredibly vulnerable to our top adversaries, but we are also so connected and so dependent on the ‘digital’ supply chain that an attack such as this can cause wide-scale damage potential.”
Supply Chain Concerns
Other analysts and cybersecurity watchers agreed with Berglas’s assessment that software and IT supply chains, along with vulnerabilities associated with third-party suppliers, remain the greatest lesson learned from this past year’s events.
Besides SolarWinds, the July ransomware attack targeted vulnerabilities in the on-premises version of Kaseya’s Virtual System Administrator, which then allowed the cybercriminals to target the company’s customers, demonstrates how the IT software community needs to work harder when it comes to creating more secure applications, said Oliver Tavakoli, the CTO at security firm Vectra.
And while software developers have been asking the right questions and trying to adapt, adversaries continue to adjust their techniques to remain that crucial step ahead.
“Much of the software development community has spent the year contemplating whether their software build and delivery infrastructure would have been susceptible to the kind of concerted effort which Cozy Bear expended on injecting code into the SolarWinds Orion software,” Tavakoli told Dice.
“Build systems have been hardened and mechanisms have been implemented to prevent unexpected software from being included in a release—call it belt and suspenders and another belt for good measure,” Tavakoli added. “Of course, the next high-profile attack will be different and there is a concern that the community not over-rotate by considering only a close replica of the SolarWinds hack. There are, after all, other ways of getting software into a vendor’s build which doesn’t involve hacking into that vendor.”
John Bambenek, a principal threat hunter at Netenrich, agreed that the success of the SolarWinds attack, especially the length of time the attackers were able to stay undetected as they moved laterally across networks, is likely to drive others to adopt similar techniques.
“SolarWinds captured the imagination of other threat groups because there just isn’t much we can really do about supply chain risk except to deploy protection technology that will detect that an adversary has found some flaw and starts doing lateral movement or other malicious activity inside a victim environment,” Bambenek told Dice.
And while supply chain attacks are becoming more sophisticated, some analysts believe organizations should take advantage of these circumstances to invest in newer technologies to increase security, as well as adopt measures such as zero trust to reduce the damage attackers can inflict even if they penetrate the network.
“The SolarWinds incident was a powerful reminder of the importance of third-party risk monitoring in security programs,” Stefano De Blasi, a cyber threat intelligence analyst at Digital Shadows, told Dice. “To improve their security posture, all organizations should not automatically grant access and permissions to third-party software and hardware. They should instead constantly verify these devices, users, and programs operating within or alongside their perimeter. The zero-trust architecture framework embodies this strategy principle that organizations should adopt to improve their security.”
Other Cybersecurity Concerns
Besides supply chain and software code cybersecurity issues, Berglas, who is now global head of professional services at cybersecurity firm BlueVoyant, noted there are three other areas of concern in the wake of SolarWinds that IT and security professionals should consider:
Network Segmentation: Part of an intelligent security posture is understanding that no tool or technology alone is going to stop a breach—organizations that prepare for a cyber threat by looking at ways to reduce the impact once they are in your network are often the ones that take the least damage.
Visibility on the Network: It is not enough to defend. Organizations need to be proactive by constantly searching for anomalous behavior in their environment—early detection of threats, coupled with a solid security posture, will help reduce the impact of an attack.
Vulnerability Assessment, Identification, and Management: These are critical parts of modern security. Attackers spend their time trying to identify holes in new software and hardware versions and then craft exploits to capitalize on those vulnerabilities. A weak vulnerability assessment and management process leaves massive opportunities for compromise.
Berglas added other cybersecurity issues also need to take center stage and “account take-overs via successful phishing campaigns due to lack of employee training; not implementing multi-factor authentication; and weak or non-existent procedures in place to assess, evaluate, and monitor trusted vendors and partners are all still present in organizations today and the leading causes of the exploitation of trust.”